RIPD The Narrative Lens for MITRE ATT&CK®
/ript/ — pronounced “ripped”
The entire MITRE ATT&CK kill chain in four phases. One glance tells you what an adversary did and how far they got.
The Four Phases
RIPD is a mobile-first lens for MITRE ATT&CK. The industry's most comprehensive threat data, powering a framework built for speed. Tap any phase to see its full MITRE mapping.
Recon
Research targets & build infrastructure
Scanning for vulnerabilities, harvesting credentials, registering domains, building attack infrastructure. No contact with the target yet — just preparation.
Infil
Gain access & execute code
First contact. Phishing email, exploited vuln, compromised supply chain, stolen creds — the adversary breaches the perimeter and runs their payload. The attack is now real.
Pivot
Persist, escalate, move laterally
Expanding the foothold. Privilege escalation, defense evasion, credential theft, network discovery, lateral movement. Often the longest phase — adversaries dwell for weeks or months.
Detonate
Exfiltrate data & cause impact
The endgame. Data exfiltration, ransomware deployment, system destruction, operational disruption. This is where the damage happens.
What RIPD Reveals
Every actor has a signature. Which phases are present — and absent — tells you the threat type at a glance.
APT28 (Fancy Bear)
Russia, Nation-stateFull kill chain. Nearest Neighbor Campaign (2022-2024) daisy-chained through nearby Wi-Fi networks for initial access. Leveraged CVE-2022-38028 zero-day during Pivot for privilege escalation.
Sandworm Team
Russia, Nation-stateDestruction-first. Ukraine power grid attacks were built to reach Detonate fast — short Pivot, maximum Impact. When Pivot is short relative to Detonate, the actor is there to break things.
Scattered Spider
Financial CrimeNotice what's missing — no Detonate. Heavy social engineering recon, SIM swapping for access, then persistent credential harvesting. They broker access, they don't detonate.
Connected Intelligence
Every kill chain phase links back through CVEs and products to the actor who exploited them — all navigable on your phone.
Bidirectional mapping — drill from any RIPD phase down into raw MITRE technique IDs, and back up again, without losing context.
See It In Action
RIPD inside CyberPrism. Tap to zoom.
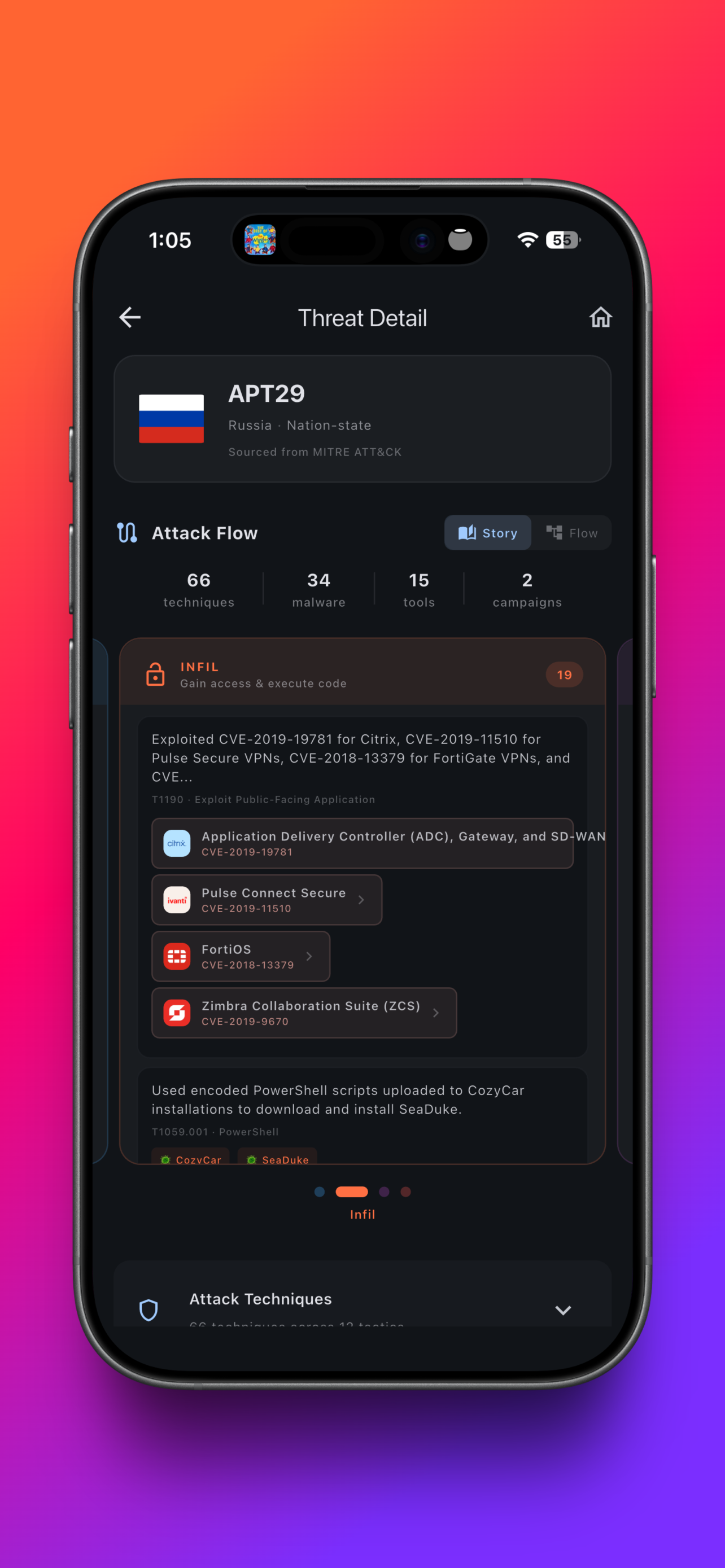
Attack Flow — APT29
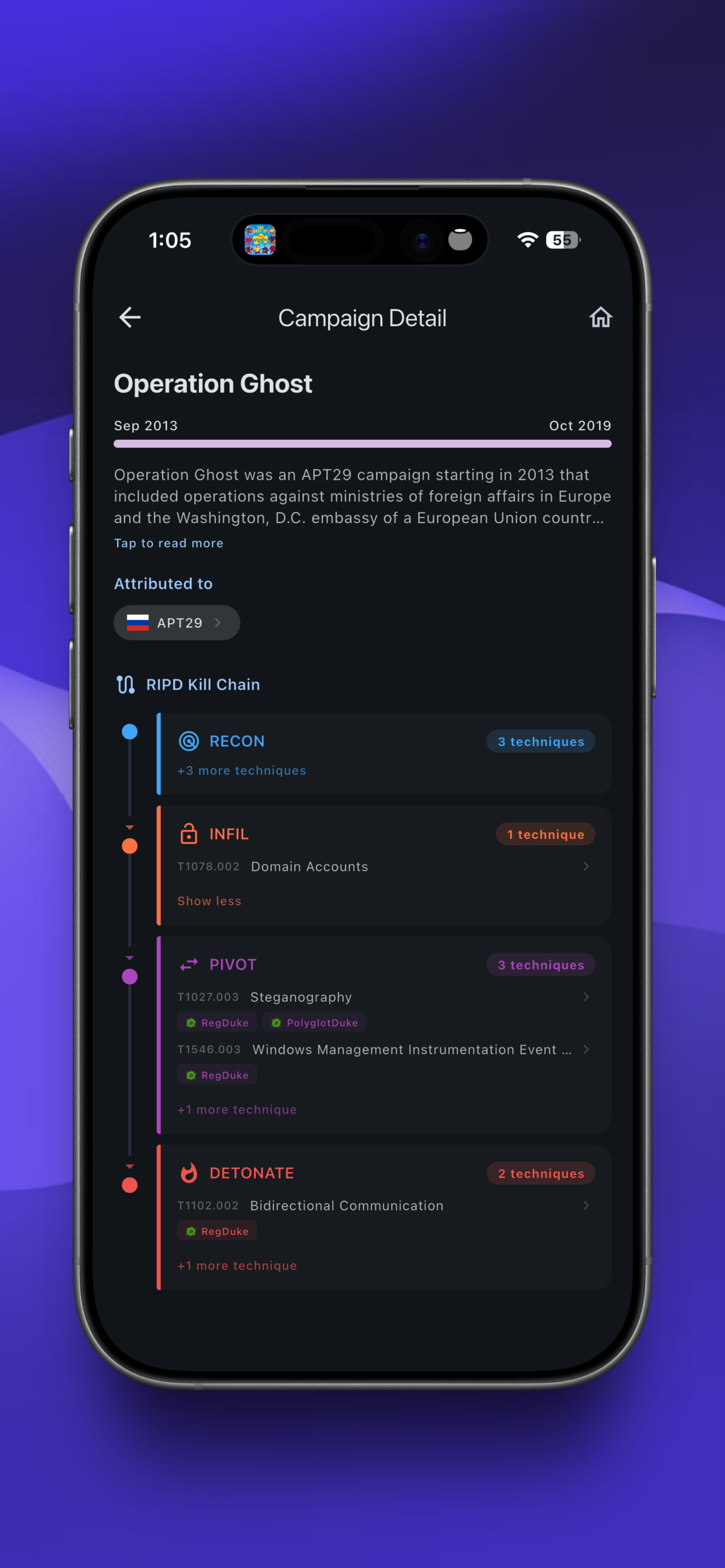
Campaign — Operation Ghost
RIPD was created by CyberPrism. Built on MITRE ATT&CK® data with full bidirectional mapping. MITRE ATT&CK is a registered trademark of The MITRE Corporation.